A Russian game has been exposed. The Security Service of Ukraine (SBU) has reported that, together with the FBI, EU law enforcement, and Polish counterintelligence, it has conducted a large-scale cyber operation against Russian military intelligence spying.
As a result, numerous cases were uncovered in which Russian special services had hacked office and home Wi-Fi routers belonging to Ukrainians and foreign citizens.
These devices, known as SOHO (Small Office/Home Office) equipment, were targeted due to outdated security protocols.
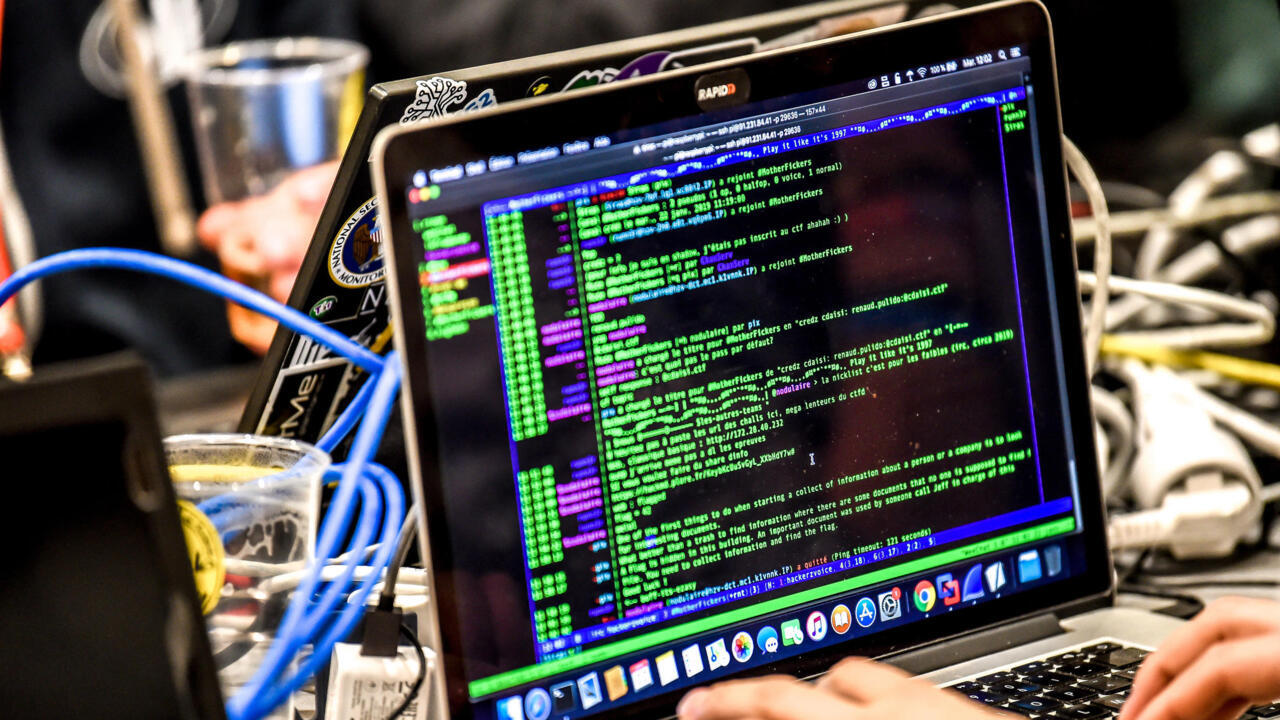
How scheme worked: routers turned into spying tools
After compromising vulnerable routers, Russian operatives rerouted traffic through a pre-established network of DNS servers, effectively turning themselves into digital intermediaries.
This allowed them to collect passwords, authentication tokens, and other sensitive data, including email communications that were normally protected by SSL and TLS protocols.
The stolen data enabled cyberattacks, information sabotage, and strategic intelligence gathering. Particular attention was given to communications of government employees, Ukrainian Defense Forces units, and defense industry enterprises.
Scale of the operation: hundreds of routers and over 100 servers reclaimed
The joint operation successfully blocked more than 100 servers and brought hundreds of routers in Ukraine out of Russian control.
This significantly weakened Russian military intelligence's capabilities and prevented potential software-level sabotage of the equipment.
"Comprehensive measures are ongoing by the SBU and its Western partners to hold all individuals involved in these cybercrimes accountable," the SBU notes.
Recommendations for users: protect your routers and data
The agency strongly advises router owners to check the model and firmware version of their devices and install all available security updates. If the manufacturer no longer supports the router, it should be replaced with a modern device.
Other critical steps include changing the access password, disabling remote management over the Internet, and checking settings for suspicious elements. Internet service providers are urged to actively support clients in implementing these cybersecurity measures.