Ukrainian OSINT communities Lex Talionis and OsintVarta published an interactive map exposing over 6,000 Russian defense industry enterprises and the personal data of 1.2 million employees, Ukrainian military news outlet Militarnyi reported on 25 February. The release — a day after the fourth anniversary of Russia's full-scale invasion — caps a multi-stage intelligence-gathering operation targeting the backbone of Russia's war machine.
Searchable map covers 6,088 factories across 85 regions
The interactive database catalogs 6,088 defense enterprises spanning 85 Russian regions, from Kaliningrad to Vladivostok. Each factory card includes a description of its activities, specific weapons and systems it develops, and a categorization system with 16 production sectors — from key component manufacturing (1,320 enterprises) and repair and modernization facilities (1,231) to radioelectronics and electronic warfare (420), aviation (399), armored vehicles (332), naval shipbuilding (314), missile and artillery systems (107), ammunition and explosives (126), and drone systems (47), among others.
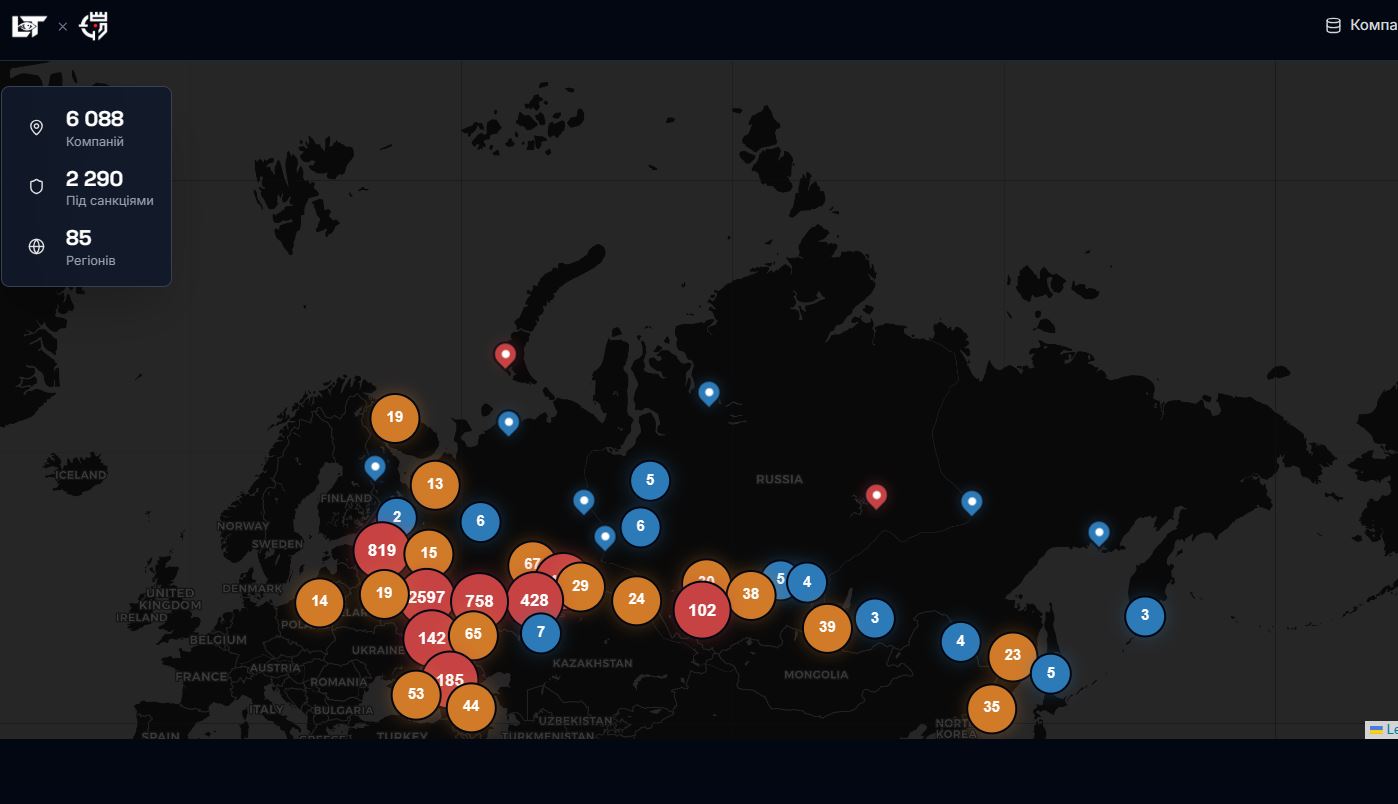
Of the 6,088 mapped enterprises, 2,290 already face international sanctions. The remaining 3,798 do not, highlighting potential gaps in Western sanctions coverage of Russia's military-industrial complex, the stats on the database's page states.
The database goes beyond factory coordinates. Hacktivists compiled personal dossiers on 1.2 million defense industry employees, including passport data, phone numbers, and email addresses of engineers, designers, and managers.
Workers at major arms producers like Kalashnikov Concern and ODK-Saturn — a manufacturer of jet engines for Russian military aircraft — lost their anonymity overnight, Militarnyi noted.
The depth of the database is visible from its structure: each of the 6,088 entries contains a description of activities, defense ministry licenses, and a full employee roster with passport data, tax identification numbers, phone numbers, and home addresses.
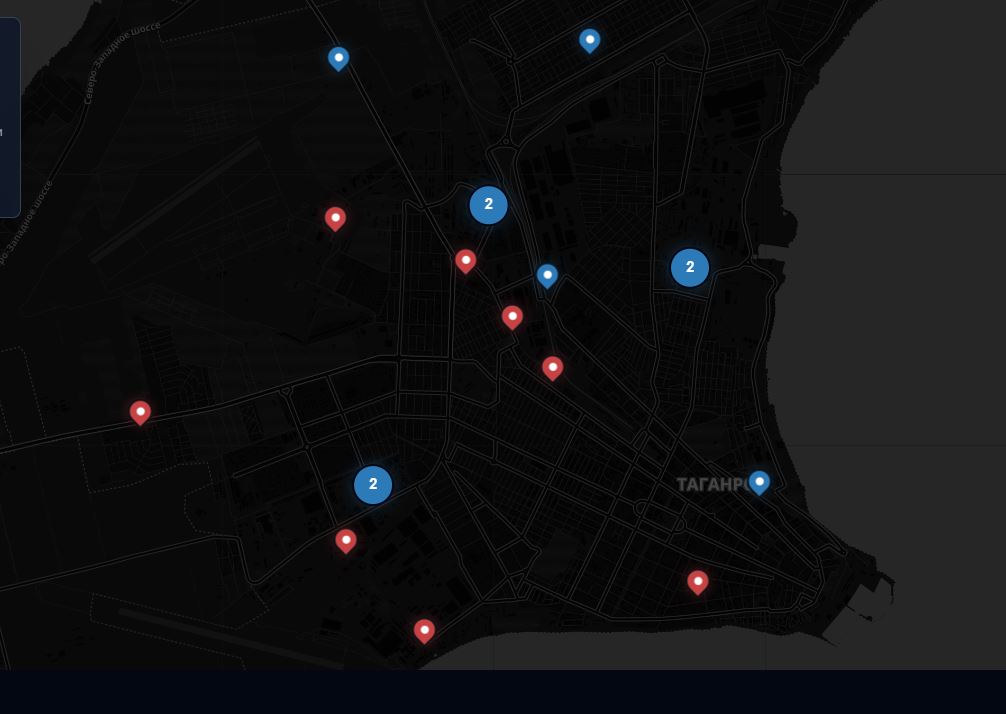
For example, one random entry, reviewed by Euromaidan Press — a Taganrog-based avionics firm, AO Beta IR — lists over 200 employees alongside its weapons and ammunition production licenses. Similar data is available for the Mil and Kamov National Helicopter Center with 3,888 listed employees, and thousands of other defense enterprises.
Hacktivists offer bounties for more classified data
The project's authors said they verified the data before publication, enabling analysts and specialists to track how Russia develops its military technologies. The employee database is freely downloadable for analytical or operational use.
Trending Now
Lex Talionis and OsintVarta did not stop at the current release. Both groups announced they are actively seeking — and offering to purchase — additional classified data on Russia's defense sector. They invited hacktivists and analysts worldwide to submit useful data dumps, internal network access, and critical documentation on Russia's military-industrial complex in exchange for payment.
"We know about you, we know what your plans are," OsintVarta wrote, addressing Russia's defense industry directly.
The groups said more updates with new facilities and system improvements are planned.

Ka-52 Alligators flew to Kyiv’s Hostomel four years ago. The companies that build and fix them still aren’t sanctioned
Ukraine's cyber campaign against Russia's defense sector
The release follows a series of Ukrainian cyber and OSINT operations that have exposed vulnerabilities in Russia's defense-industrial base. Ukrainian hackers and OSINT groups have ramped up operations against Russian military infrastructure throughout the war.
- In February 2026, Ukrainian hackers set up fake Starlink activation channels that collected intelligence on Russian units while pocketing their cryptocurrency payments.
- Im late January, Militarnyi reported that Russian journalists obtained a large trove of internal documentation from the Yantar Baltic Shipbuilding Plant in Kaliningrad.
- In December 2025, cyber specialists from Ukraine's Defense Intelligence and the BO Team erased 165 terabytes of data from Eltrans+, a logistics firm shipping sanctioned Chinese electronics to Russian missile factories.
- In November 2025, InformNapalm shared classified documents from next-gen strategic bomber program showing that Western sanctions delay the development.
- In July 2025, HUR operatives downloaded 100 terabytes of classified military data from occupied Crimea before destroying the originals.
- In June 2025, InformNapalm and Militant Intelligence leaked internal contracts of JSC Russian Helicopters, exposing foreign supply routes through Egypt, India, and Bulgaria.
Read also
-
The plant makes ammonia and ammonium nitrate. The Russian army turns them into TNT and RDX. Ukraine just set it on fire — again
-
Russia used Belarus’s cell towers to bomb Ukrainian power plants. Then hackers got inside the operators’ chatrooms
-
Ukraine’s cyber warriors crush Russian control systems in Crimea, steal 100TB of secrets


