Ukrainian hackers infiltrated Russian drone operator systems for six months, exposing how Russia weaponized Belarusian civilian infrastructure to strike Ukraine and test attack routes into NATO countries, InformNapalm reported on 20 February.
Since Russia started its full-scale invasion of Ukraine in 2022, Belarus has been Moscow's closest ally in the war, having let Russian forces cross its territory toward Kyiv at the invasion's outset and continuing to provide matériel support and training ever since.
Hackers broke into dozens of Russian military accounts
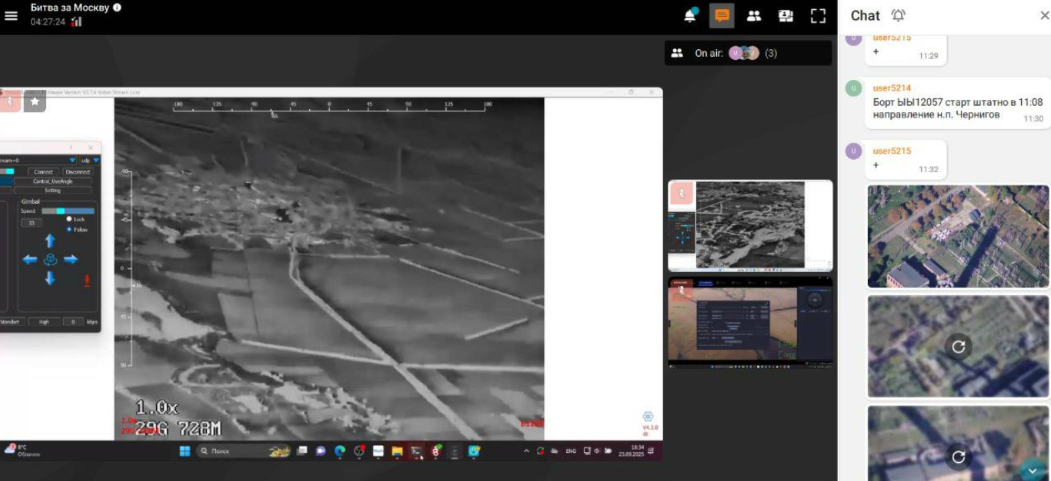
The cyber operation was carried out by hackers from the Fenix analytical cyber center with support from InformNapalm volunteers. The team broke into accounts of dozens of Russian military personnel and gained access to monitoring systems used by attack drone operators, InformNapalm says. They organized round-the-clock covert surveillance, carefully hiding their presence.
The hackers could not control the drones. But they could watch every move — flight paths, flight missions, and internal chats. They promptly passed all data to Ukraine's defense forces, helping intercept Russian drones more effectively. The operation ran from at least mid-2025 through February 2026, when it exhausted its intelligence potential — partly because of Ukraine's own successful strikes that the surveillance had enabled.
Belarus's cell towers turned into drone highways
Analysis of intercepted chats revealed Russia was using Belarusian civilian cell towers to route strike drones, providing stable signal along the border and extending strike range range to targets near northern and western Ukraine's borders. Russia also deployed signal repeaters on Belarusian territory in the second half of 2025, reaching targets from Kyiv Oblast to Volyn. Some attacks on energy and railway infrastructure would not have been possible without this assistance, Zelenskyy noted when announcing the sanctions.

Surveillance enabled strikes on Russia's elite Rubikon unit
According to InformNapalm, Ukraine's defense forces used the intelligence for strikes on command posts and drone launch sites in Russian territory and occupied areas. The data also enabled strikes on positions of the elite Rubikon drone unit — a formation established in August 2024 and widely considered one of Russia's most effective battlefield units.
Poland drone incursion was a deliberate test, hacked chats show
One of the operation's most significant findings concerned the September 2025 drone incursion into Poland. Overnight on 9-10 September, at least 19 Russian drones entered Polish airspace, triggering NATO's first live-fire response since the full-scale invasion began. Russia claimed the drones simply strayed during strikes on Ukraine.
Trending Now

Russians paid crypto to restore Starlink. Ukrainian hackers took the money – and the data
InformNapalm says the hacked chats tell a different story. Ukrainian hackers passed intelligence to NATO partners as early as September 2025, showing the incursion was a test of Belarusian cellular infrastructure capabilities. Russia's goal was to plan future strikes on logistics routes in both Ukraine and Poland — to cut Western weapons deliveries.
Physical evidence corroborates the findings. Russian operators' software and chats contained data about YY-series drones. Gerbera decoy drones with serial numbers YY32384 and YY31402 were later found in Poland. A tail fragment of YY31704 washed up on a beach in Latvia.

Sanctions on Likashenka and the stalled Cyber Forces bill
Zelenskyy announced the sanctions on 18 February, accusing Likashenka of "trading Belarus's sovereignty for the continuation of his personal power." Beyond drone relays, he pointed to over 3,000 Belarusian enterprises supplying Russia's military and ongoing construction of Oreshnik missile infrastructure in Belarus.
A recent successful operation against Russia's attempts to bypass Starlink blocking demonstrated the potential of civilian-military cyber cooperation — but InformNapalm argues the potential is far greater with proper institutional backing.


